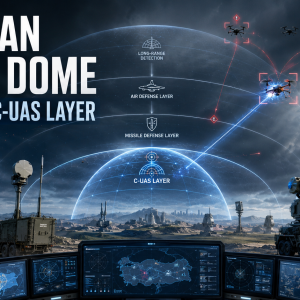
In an era of rapid technological advancement, Safeguarding Autonomous Vehicle Networks have emerged as the frontrunners in revolutionizing the way we navigate our world. From self-driving cars that navigate bustling city streets to unmanned aerial vehicles (UAVs) that soar through the skies, and autonomous sea vessels that explore uncharted waters, these cutting-edge technologies are reshaping the future of transportation across land, air, and sea.

As autonomous vehicles become more prevalent, it is essential to safeguard their networks from cyberattacks. These networks are vulnerable to a variety of threats, including hacking, data privacy breaches, GPS spoofing, and software and hardware vulnerabilities.
To address these threats, it is important to implement multiple layers of security, such as encryption, authentication, intrusion detection systems, over-the-air updates, multi-factor authentication, and redundancy and fail-safes. By taking these steps, we can help to ensure that autonomous vehicle networks remain safe and reliable.
In this blog post, we will discuss the importance of safeguarding autonomous vehicle networks and the measures that can be taken to ensure secure mobility in an increasingly connected world.
The Rise of Autonomous Vehicle Networks
Autonomous vehicles are rapidly gaining popularity, with applications in a variety of industries, including transportation, logistics, and defence. These vehicles rely on complex software and communication systems, which makes them vulnerable to cyberattacks.
Potential Threats to Autonomous Vehicle Networks
Some of the potential threats to autonomous vehicle networks include:
- Hacking and unauthorized access: Malicious actors could exploit vulnerabilities in the software or communication systems of autonomous vehicles to take control of the vehicles, causing accidents, theft, or even acts of terrorism.
- Data privacy breaches: Autonomous vehicles collect vast amounts of data about their surroundings and passengers. This data could be used to track individuals’ movements or to commit identity theft.
- GPS spoofing and jamming: Manipulating GPS signals could cause autonomous vehicles to deviate from their intended paths or to lose communication with control centres.
- Software and hardware vulnerabilities: Flaws in the software or hardware of autonomous vehicles could be exploited by malicious actors to cause system failures or to take control of the vehicles.
Safeguarding Autonomous Vehicle Networks
To address these potential threats, it is important to implement multiple layers of security for autonomous vehicle networks. Some key measures include:
- Encryption and authentication: Employing robust encryption and authentication protocols helps to protect data from unauthorized access and ensures that only authorized users can control and communicate with the vehicles.
- Intrusion detection systems (IDS): Implementing IDS on the network helps to identify and respond to potential cyber threats in real-time, enabling swift action to mitigate risks.
- Over-the-air updates: Regular software updates are crucial to patching vulnerabilities and strengthening security. Over-the-air updates enable the efficient and widespread distribution of the latest security patches.
- Multi-factor authentication: Implementing multi-factor authentication for access to critical systems adds an extra layer of security, reducing the risk of unauthorized control.
- Redundancy and fail-safes: Building redundancy into the vehicle systems allows for fallback mechanisms in case of cyber attacks or system failures.
Conclusion
Autonomous vehicle networks hold immense potential to revolutionize transportation and mobility across land, air, and sea. However, to fully embrace this technological shift, we must prioritize cybersecurity and take proactive measures to safeguard these networks against potential threats. By adopting robust security practices, encryption, and continuous updates, we can ensure that autonomous vehicle networks remain a safe, reliable, and transformative mode of transportation for a connected world.